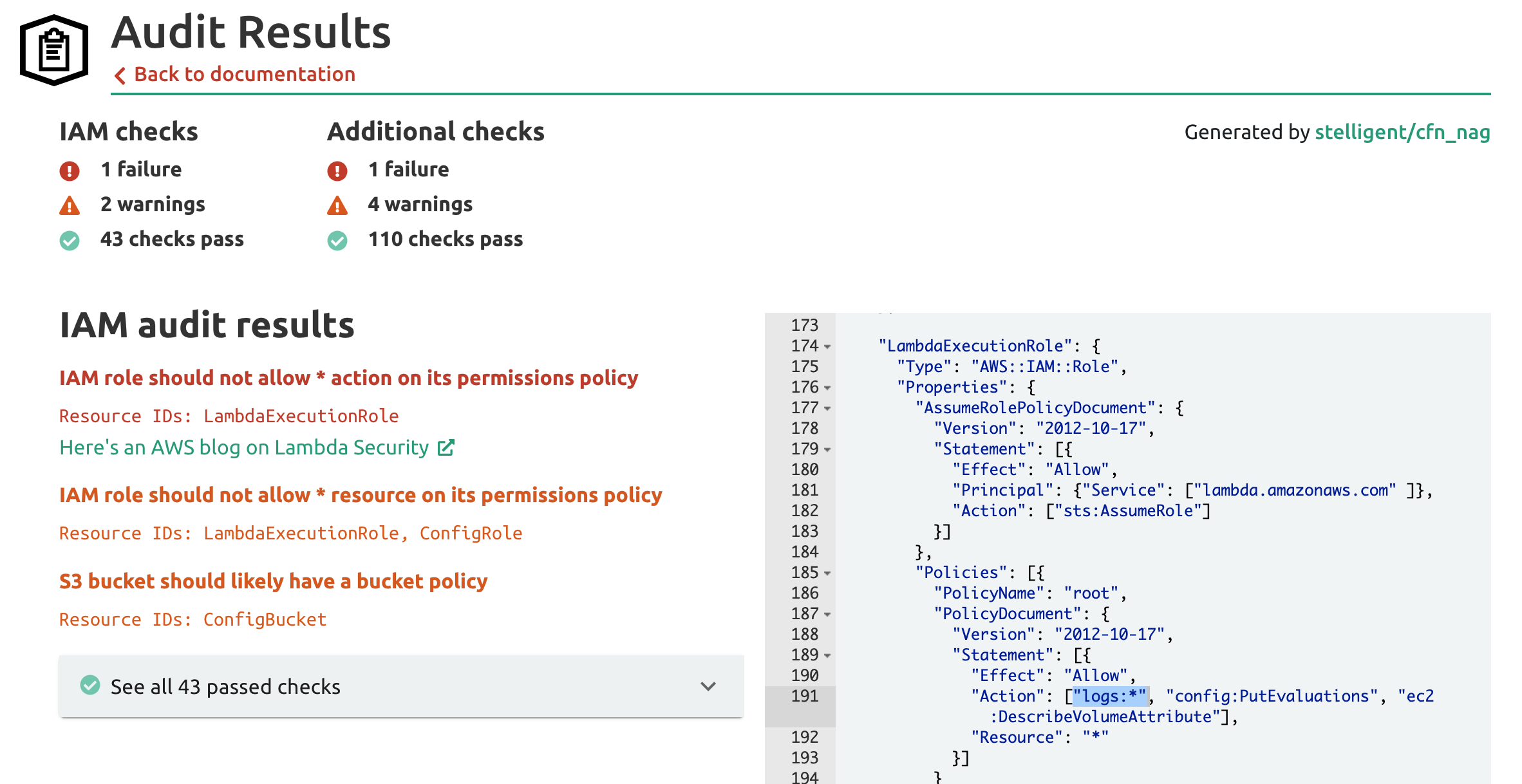
Unit 42 Cloud Threat Report: Misconfigured IAM Roles Lead to Thousands of Compromised Cloud Workloads

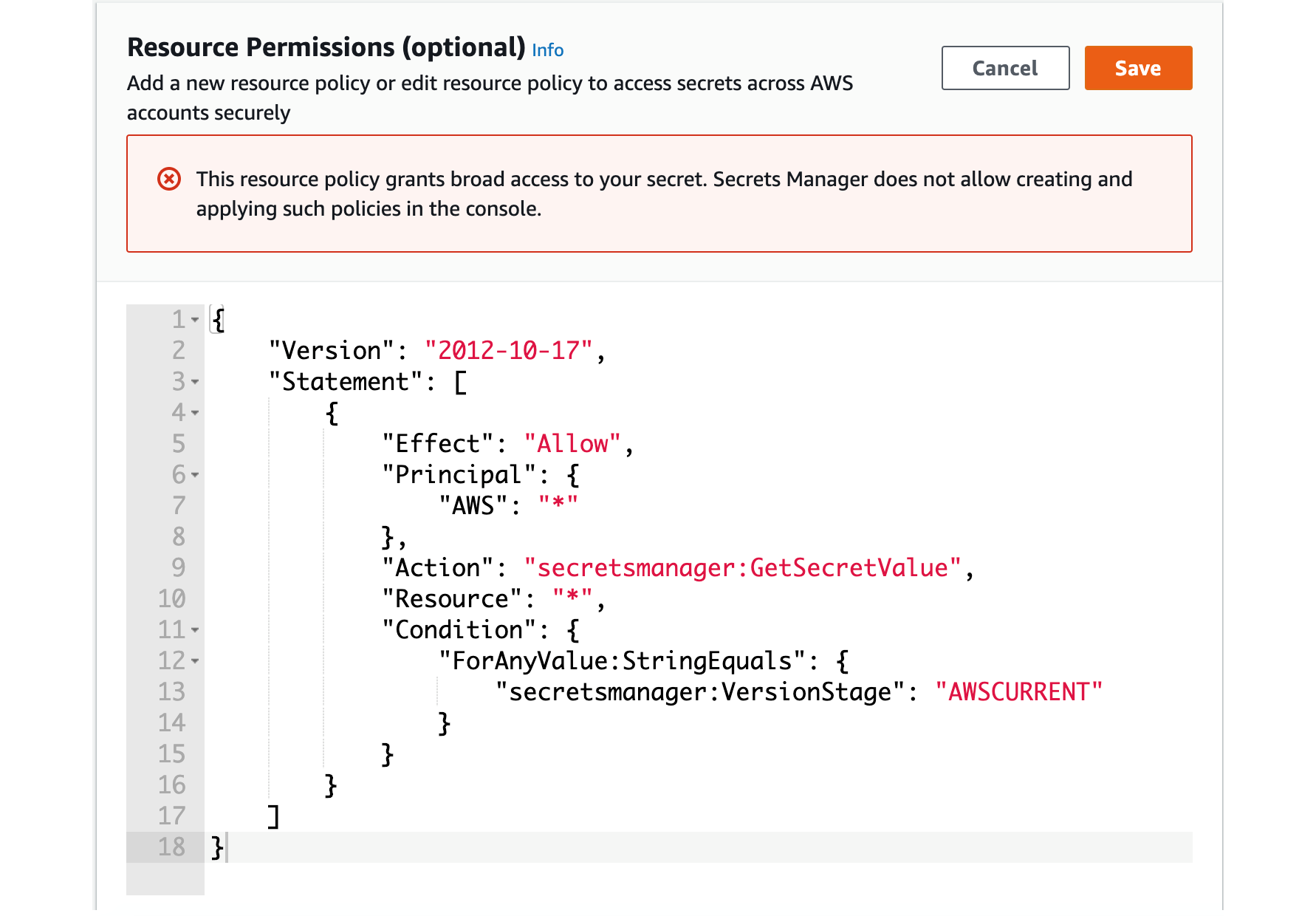
How to use resource-based policies in the AWS Secrets Manager console to securely access secrets across AWS accounts | AWS Security Blog

How to use resource-based policies in the AWS Secrets Manager console to securely access secrets across AWS accounts | Noise