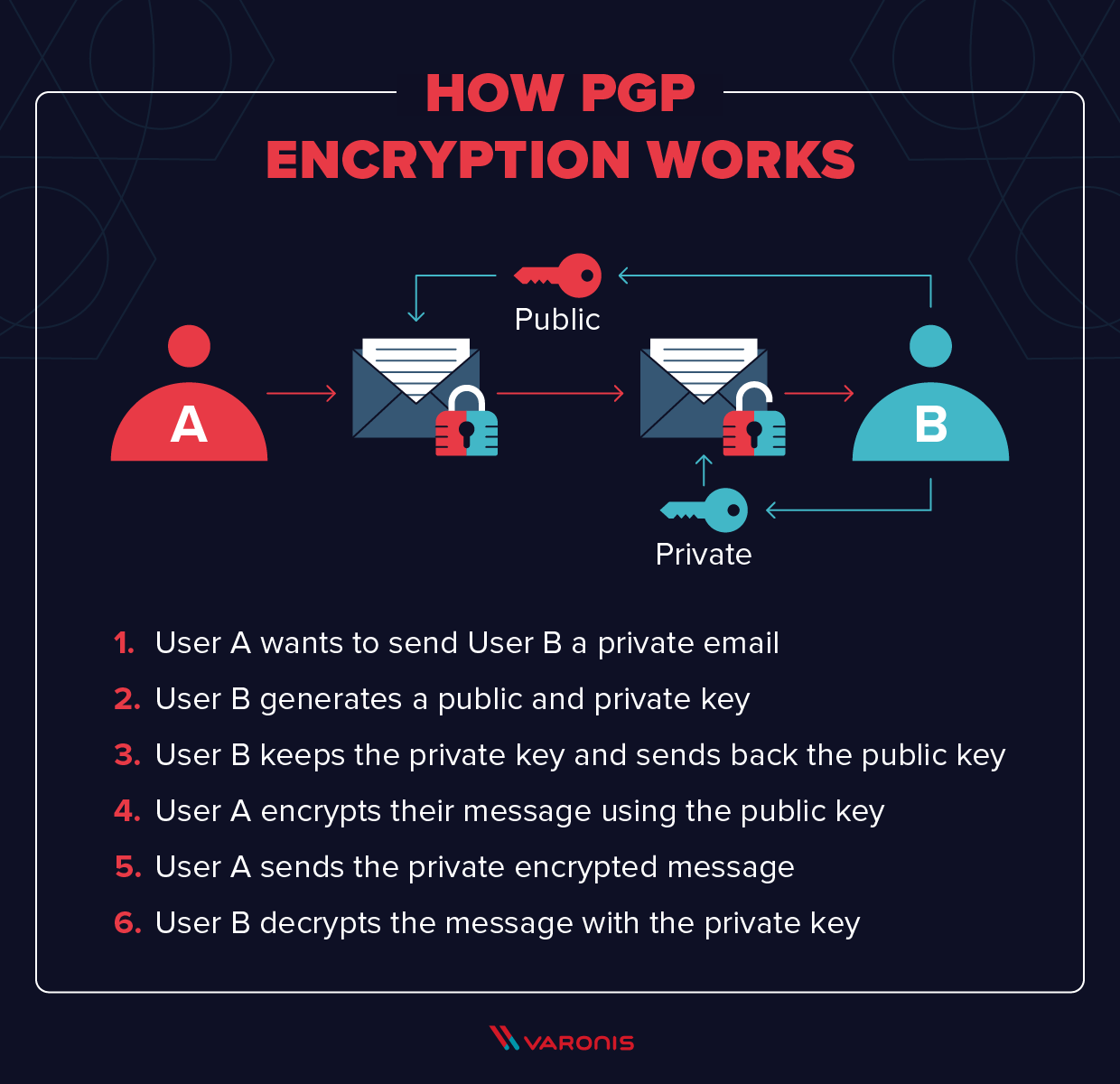
A Deep Dive on End-to-End Encryption: How Do Public Key Encryption Systems Work? | Surveillance Self-Defense
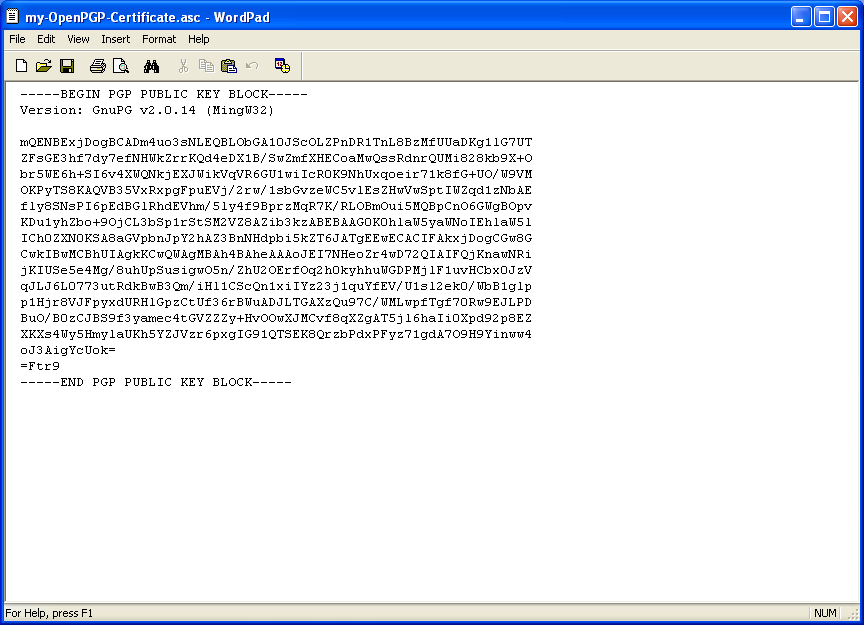
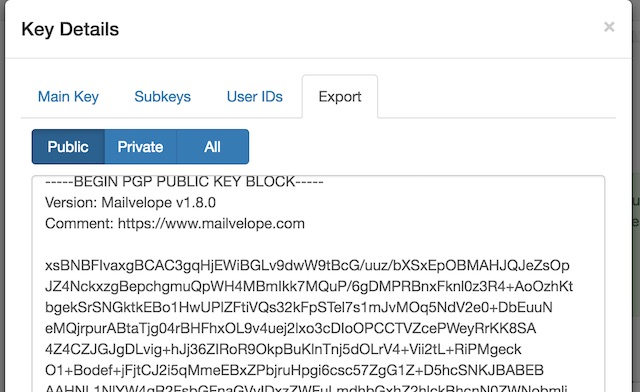
pgp - Why is GnuPG changing first two characters of ascii armored public key after downloading it from the key server? - Cryptography Stack Exchange